Search Replace DB for Databases
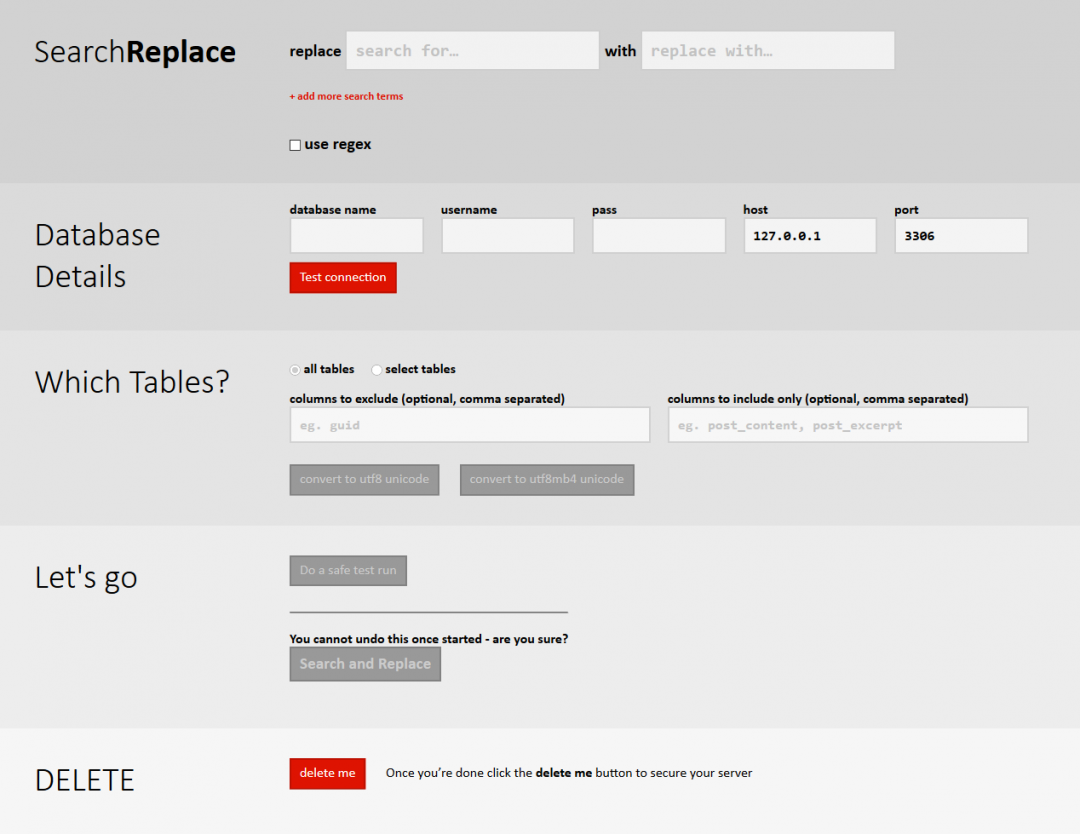
Our developer focussed tool allows you to quickly and effectively replace content, data and items in any MySQL or compatible database whilst safely handling serialised PHP strings.

Download Search Replace DB
We store your data in order to confirm that you have acknowledged the risks in using power tools such as this. We do not use it for marketing. If you were previously signed up to our newsletter, this is not currently active.
"*" indicates required fields
For how we use your data, please see our privacy policy.
How to install
Download the script from the link you received by email, and install it to a secret folder with an obfuscated name if used on a public facing server. Your server should also not be set to provide directory lists if it's a public server.
Do not install Search Replace DB to the root folder or you risk all sorts of potential problems. Just don't. It must run in its own folder and ideally one that can't be easily guessed.
To see how you can use this tool to aid migrations, check out our article on WordPress migrations or visit the WP Tuts+ article that mentions this script.
If you are in any doubt whatsoever about how to use this standalone script, then please consider getting an expert or strong IT support involved.
Licensed under GPL v3
The code is supplied under the GPL V3 and is fully open source. Do be aware that this means people can change this code and offer it up, and that other versions may be worse... or better. It is code for developers, by developers, and you should only use code from sources you trust.
FAQs
Where do I install the unzipped files?
In a directory on your webserver. It can be an httpauth protected folder if it's a public facing webserver.
Do I have to pay?
No, this is free open source and you can find it on GitHub. You can also do things like send copies of it to your friends, or use the code in other projects. The full license is included in the software. We make the default path one of letting you make a donation, but if you're skint and you work in one of those corporates where getting approval for a $5 spend isn't worth the hassle, you can grab. Just remember us if the script makes you look good and gets you a raise!
I heard this script is insecure. Is it really?
Not as dangerous as it used to be! For convenience, we picked up the WP config variables to prefill the database details. Problem with that is that it turns out people are careless and would leave the script lying around on their production facing server. So that had to go. Convenient for dev installs, nightmare on a production server. It's still a powerful tool, and it gives access to a hacker to try and brute force your database credentials, so it's really important that you don't just leave the script lying around still, but if you are using this on production servers and you are a bit absent minded then you won't be punished by getting hacked quite so easily.
I get an error 2: Class __PHP_Incomplete_Class has no unserializer
This is a common error and generally comes up with users of Yoast plugins, but also some others. It's something we're aware of. In the vast majority of cases everything is fine. You could try running the script from a different PHP install - there is no reason why you can't have a pipe to a production database and connect to it from your workstation, for example. We've done our best to ensure that the script A little more detail is on our github repository.
Changelog:
We no longer publish the changelog on this page - you can view it at Github.
Contributions
We'd love to get contributions, bug reports and more on the Search Replace DB github repository. Please come on over - you'll be more than welcome but you will need to request access by emailing [email protected]
We'd like to thank everyone in the past who has sponsored this tool and given us the ability to continue to improve it and release it for free. Every penny counts. The code and algorithm is also reused in WP-CLI, making it one of the most used tools by developers across the world.